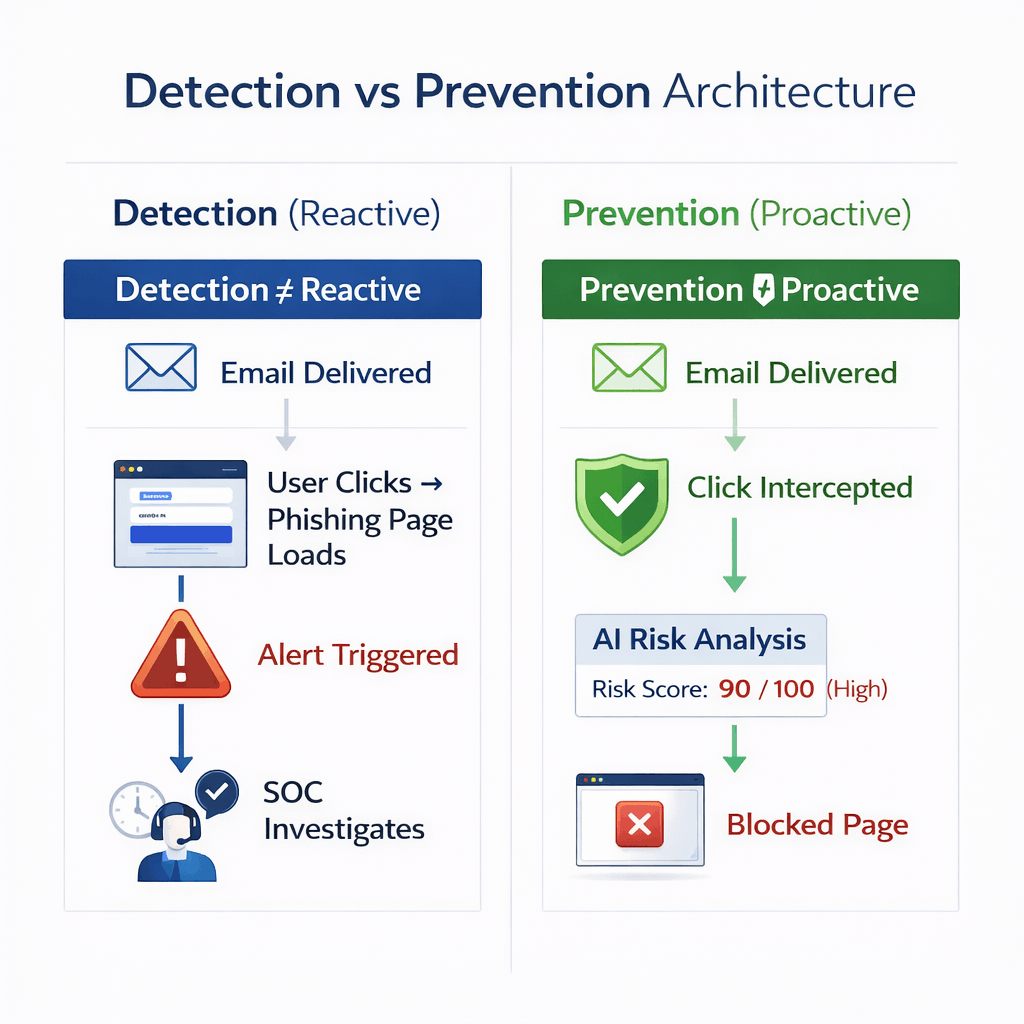
In the context of phishing protection, the difference is not semantic. It determines whether an organization blocks an attack before damage occurs or responds after exposure.
This section explains the architectural differences between reactive filtering systems and proactive prevention frameworks, and why prevention-first security models are replacing legacy detection-based approaches.