Real-Time Phishing Detection with Structured Security Events for SIEM and SOC Workflows.
Phishing has become the primary entry point for modern cyber attacks.
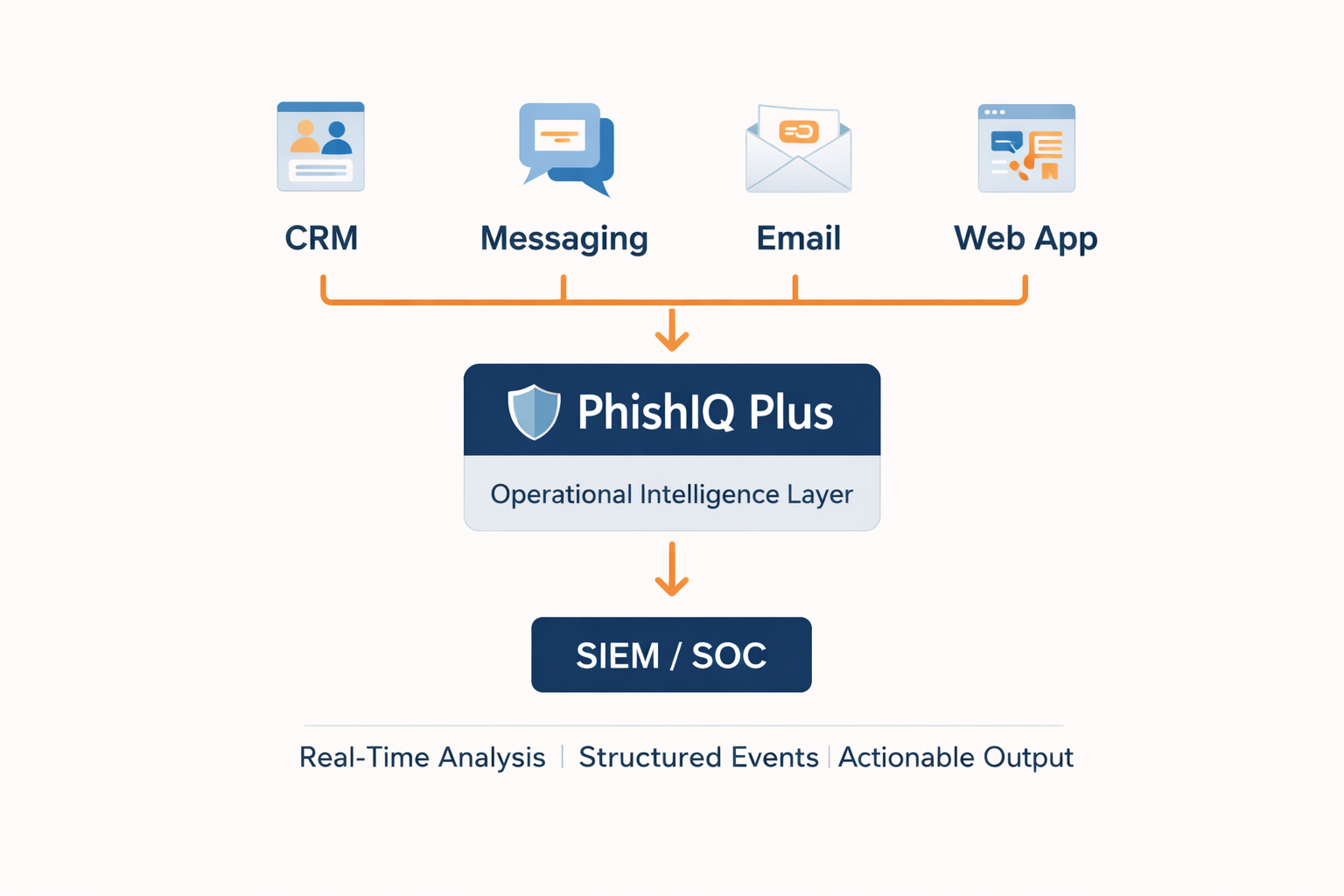
PhishIQ Plus is designed for enterprise security teams that need phishing detection beyond single URL analysis, with direct integration into monitoring and operational environments.
PhishIQ Plus delivers enriched, risk scored, structured phishing events in JSON format, optimized for direct ingestion into SIEM systems such as Splunk and Microsoft Sentinel, and SOC investigation workflows.
While PhishIQ API is intended for in app integration during development, PhishIQ Plus is purpose built for centralized monitoring environments, adding an operational security layer within the enterprise security architecture.
Suspicious links originate from a wide range of sources.
Customer service platforms, messaging systems, CRM environments, internal applications, collaboration tools, and external communication channels.
Most organizations have basic detection capabilities - but often lack a dedicated layer that provides:
- Clear security context
- Accurate risk scoring
- SIEM-ready event formatting
- Correlation capability with existing logs
- Efficient analyst prioritization
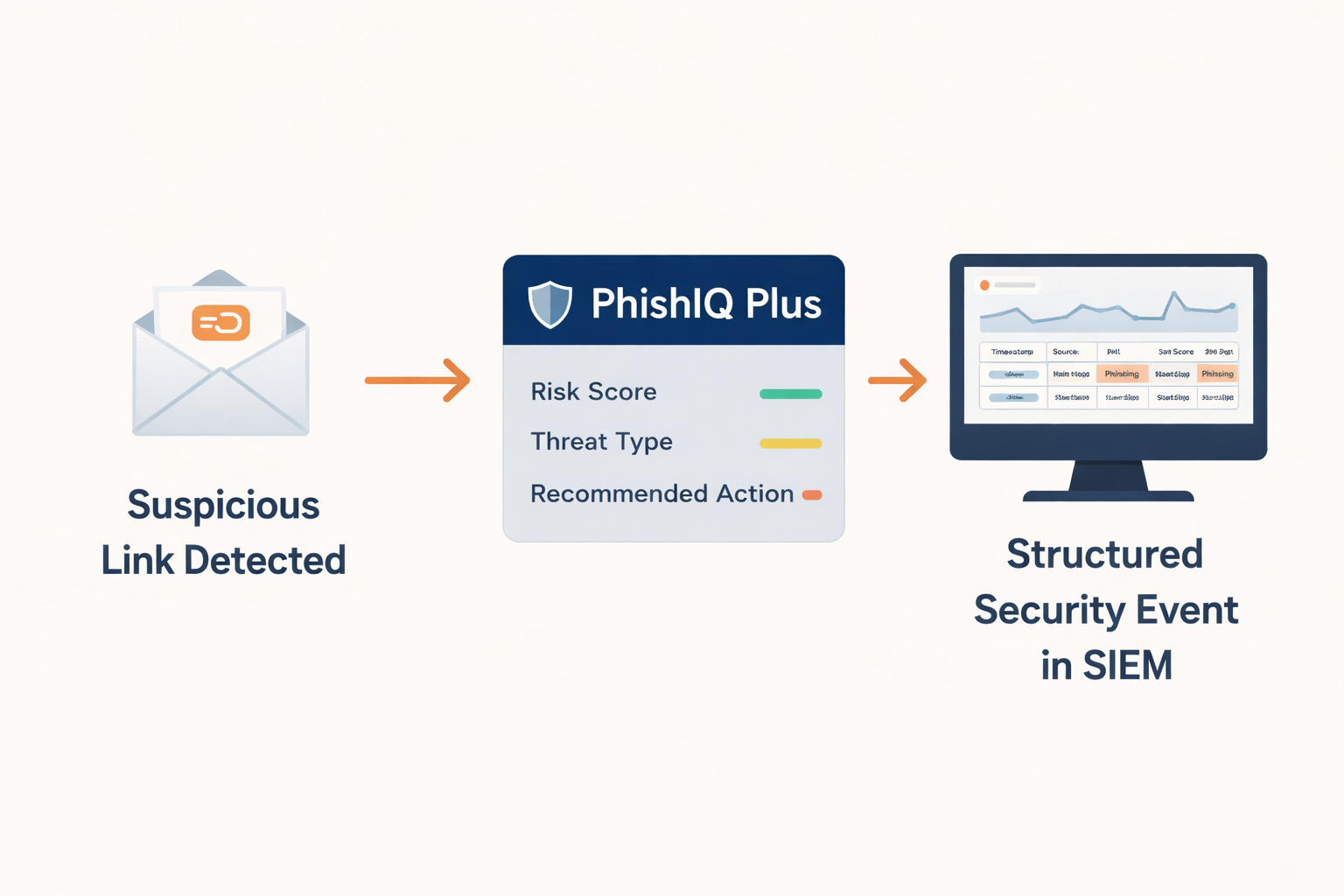
Turn phishing alerts into SIEM-ready security insight.
Without structured event data and enriched threat intelligence, phishing alerts create operational noise instead of actionable security insight. PhishIQ Plus extends the PhishIQ detection engine into a fully operational capability for SOC teams.
Every submitted link undergoes real-time AI-driven analysis, fraud pattern and behavioral detection, threat classification, risk score calculation, and generation of a structured security event - requiring no additional processing or manual interpretation.
Key Benefits
Real-Time Phishing and Fraud Detection
Every URL is analyzed instantly using advanced AI models that identify phishing attempts, impersonation campaigns, credential harvesting pages, and fraud infrastructure before damage occurs.
Intelligent Detection of Unknown and Evasive Links
Detects previously unseen threats by analyzing link structure, behavioral patterns, content signals, and contextual indicators - not just reputation databases - enabling protection against zero-day phishing campaigns.
Advanced Redirect and Obfuscation Resolution
Fully resolves shortened URLs, multi-layer redirect chains, CDN-based links, and masked destinations to uncover the true final landing page behind complex attacker techniques.
Support for Dynamic and Restricted Links
Handles time-sensitive URLs, single-use tokens, deep links, and dynamically generated redirects, ensuring reliable detection even when attackers use sophisticated access restrictions.
Clear Risk Scoring and Automatic Prioritization
Provides transparent risk scoring logic that enables SOC teams to prioritize incidents efficiently and focus on high-impact threats.
Structured JSON Security Events
Returns enriched, SIEM-ready JSON responses including risk score, threat classification, safety status, recommended action, and technical indicators - eliminating the need for manual interpretation.
Native Alignment with SIEM and SOC Environments
Designed specifically for centralized monitoring architectures, enabling direct ingestion into SIEM platforms and seamless integration with existing SOC workflows.
High-Throughput, Low-Latency Performance
Built to support enterprise-scale environments, processing high volumes of URLs without disrupting operational workflows or creating bottlenecks.
Flexible Deployment Options
Available for cloud, private cloud, and hybrid environments, allowing organizations to integrate phishing detection within their existing security architecture.
Privacy-First Architecture
Operates under a strict Zero Data Retention policy. Submitted URLs and metadata are analyzed in real time and immediately discarded, supporting GDPR and enterprise privacy requirements.
Primary Use Cases
SOC Teams
Stream enriched phishing events directly into SIEM platforms such as Splunk and Microsoft Sentinel for investigation, prioritization, and correlation with broader security telemetry.
SIEM-Centric Architectures
Enhance existing monitoring infrastructures with a dedicated phishing intelligence layer without replacing current security tools.
MSSPs
Provide a unified phishing detection layer across multiple clients with standardized event structures optimized for monitoring platforms.
Hybrid Security Environments
Add advanced phishing detection capabilities without modifying existing infrastructure or workflows.
How PhishIQ Plus Works
1. A system generates an event containing a suspicious link.
2. The event is sent to PhishIQ Plus.
3. Real-time analysis and threat intelligence enrichment are performed.
4. A structured security event is generated, including risk score and threat classification.
5. The event is streamed directly into the SIEM or SOC workflow.
No workflow redesign required.
No intermediary tools needed.
Technical Specifications
- SIEM-Optimized Event Output Generates structured security events designed for direct ingestion into enterprise SIEM platforms.
- Real-Time Event Streaming Capability Supports secure event delivery into monitoring pipelines without requiring architectural changes.
- High-Volume Processing Architecture Designed to handle enterprise-scale link analysis across distributed environments.
- Low-Latency Operational Performance Enables near real-time threat visibility suitable for active SOC monitoring.
- Flexible Deployment Models Available for cloud, private cloud, or hybrid environments based on organizational security and compliance requirements.
- Secure Integration Framework Supports secure authentication, encrypted communication, and controlled access policies.
- Scalable Enterprise Architecture Built to operate reliably across large, multi-region infrastructures.
- Privacy-First Processing Operates under a strict Zero Data Retention model aligned with regulatory requirements.
How Is It Different from PhishIQ API?
PhishIQ API is designed for developers who want to embed phishing detection directly into applications, websites, or internal systems during product development.
PhishIQ Plus is built for operational security environments. It focuses on structured security event generation, prioritization, and SOC-level management.
Both products are powered by the same core detection engine but are optimized for different integration models and enterprise use cases.
Ready to Elevate Your Security Operations?
Contact us to learn how PhishIQ Plus integrates seamlessly with your SIEM environment and delivers actionable phishing intelligence directly into your SOC workflows.


