Advanced Protection. Simple Integration. Real-Time Performance.
Phishing attacks against organizations are not new, but in recent years they have grown in frequency, complexity, and sophistication.
Recent studies show an annual rise of approximately 30%–50% in phishing attacks. Attackers use AI to craft convincing emails and messages that bypass traditional defenses and cause substantial damage.
of organizations have experienced phishing in the past 5 years
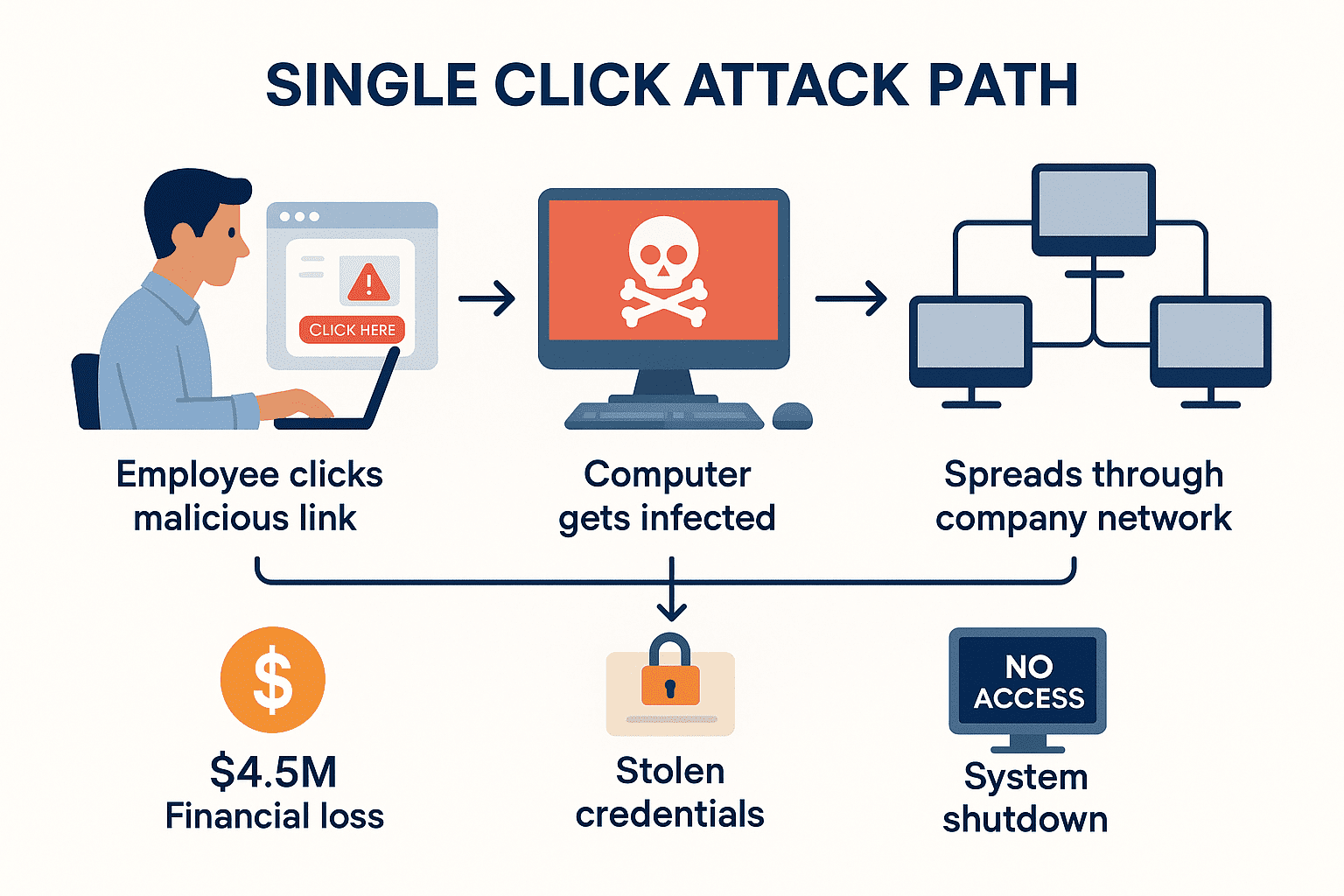
The total cost of a phishing attack - recovery, penalties, reputational damage - ranges between $4.5M and $4.9M.
Business Email Compromise (BEC) attacks cause severe losses. Without real-time detection, a single incident can mean regulatory penalties, operational shutdowns, and lasting reputational harm.
click
The vast majority of breaches start from human error - most often, one click on a malicious link.
That single click by one employee is the critical point that lets attackers in. Without real-time monitoring, it can cripple an entire organization.
This is exactly what PhishIQ delivers.
When teams rely only on traditional solutions (like blocklist-based filtering), they miss the power of AI operating in real time - and the chance to use AI as a defensive tool. Bad actors weaponize AI to deceive and exploit; security teams can use it to stay one step ahead. PhishIQ enables organizations to integrate advanced phishing and fraud detection via a fast, easy-to-implement API with full documentation - built on the same engine as the RedFox app, scaled for enterprise.
Key Benefits
Real-Time Link Analysis
Every URL sent to the API undergoes immediate analysis within 50-150 milliseconds, including full redirect resolution, malicious destination checks, and cross-referencing with continuously updated threat databases containing over 500 million known threats.
Intelligent Detection of New and Unknown Links
AI and machine learning algorithms analyze each link's structure, behavior, content, and context - even if the link is not yet in any database - to identify suspicious patterns and sophisticated fraud attempts with 97.6% accuracy rate.
Support for Shortened and Obfuscated Links
Includes resolving redirects and examining the actual final landing page - even for shortened, masked, or CDN-served URLs. Successfully handles 15+ redirect layers and decodes complex obfuscation techniques.
Support for Smart and Special Links
Handles time-limited URLs, single-use tokens, deep links and dynamic redirects - ensuring protection even when attackers use advanced link restrictions.
Works Across All Platforms
Protects users whether they click links in emails, text messages, social media, or any digital communication channel - one solution covers everything.
Instant Decision Making
No waiting, no delays - immediate "Allow/Block/Warn" recommendations help your team make quick security decisions without disrupting workflow.
Industry standards compliance
Meets recognized security standards, industry best practices, and regulatory compliance requirements across multiple sectors.
Detailed, Smart Response
The API returns a comprehensive JSON response including risk score, threat type identification, safety status, recommended action, and additional technical details. Process over 10 million URLs hourly with consistent performance.
Flexible Custom Parameters
Each API request can include additional tracking identifiers, department codes, user IDs, or any custom metadata. All parameters are returned unchanged with the analysis results, enabling seamless integration with existing audit systems, user tracking, and organizational workflows without requiring separate correlation processes.
Real-Time SIEM / Dashboard Integration
Seamlessly push PhishIQ threat intelligence and risk scores directly into your existing SIEM or security dashboards for immediate, centralized monitoring and automated response.
Full GDPR Compliance & Privacy Protection
Zero data retention policy - all submitted URLs and metadata are analyzed in real-time and immediately discarded, ensuring complete compliance with European privacy regulations while maintaining full security effectiveness.
Zero False Positives
Advanced algorithms ensure legitimate business links are never blocked, maintaining smooth user experience while blocking real threats.
Easy Customer Protection
Protect your customers effortlessly by integrating PhishIQ into your website or app, enhancing security and confidence in your services.
24/7 Automated Protection
Continuous monitoring means threats are detected and blocked even outside business hours, weekends, and holidays.
Primary Use Cases
Telecommunications and Mobile Providers
Real-time filtering of malicious links in SMS messages, WhatsApp, Facebook Messenger, Telegram, and other digital channels. Protect millions of subscribers simultaneously with instant analysis of shortened URLs and redirect chains commonly used in smishing campaigns.
Financial, Commercial, and Healthcare Apps
Prevent users from navigating to phishing sites that mimic your services, protecting sensitive credentials and personal data. Add an extra security layer when users click external links, with risk scoring and instant recommendations for safe browsing.
Managed Service Providers (MSPs)
Integrate PhishIQ API into your managed services platform to offer clients real-time phishing protection. Expand beyond infrastructure management by preventing ransomware, data breaches, and financial fraud at the source.
Security Operations Centers & MSSPs
Enhance your security stack with specialized API-based phishing detection. Fill coverage gaps in communication channels and endpoints that traditional security tools miss, while maintaining centralized threat monitoring.
Service Centers / Helpdesk Systems
Automatically analyze suspicious links received through customer chats, support tickets, and internal communication systems. Prioritize security incidents based on threat levels and maintain audit trails for compliance and investigation purposes.
MDM / Enterprise Security Systems
Integrate with mobile device management and corporate security frameworks to monitor employee browsing behavior. Track threats by department or user groups using custom parameters, and enhance existing SIEM systems with detailed threat intelligence data.
How It Works
1. Submit a URL for inspection to the PhishIQ server.
2. Receive an immediate response including:
- Risk level rating
- Phishing/fraud attempt detection
- Technical and behavioral information
- Recommended action (Allow / Warn / Block)
3. Decide on the appropriate action based on the result - block, warn, or allow normal access.
Technical Specifications
- REST API with JSON format
- SLA of 99.99% availability
- Support for high throughput
- Latency up to 150ms
- Multi-platform compatibility
- Full GDPR compliance with zero data retention
- Support for shortened URLs, Smart-Links, redirects, and CDN networks
Why Choose PhishIQ?
- Proven Track Record Powers the RedFox app with millions of active users already protected
- Future-Proof Technology Evolves with emerging threats while attackers adapt their methods
- Cost-Effective Protection Prevent expensive security incidents before they happen
- Competitive Advantage Stay ahead of organizations still relying on outdated signature-based detection
- Regulatory Compliance Support Helps meet security requirements across different industries
- Scalable Architecture Grows with your organization from startup to enterprise without performance degradation
- Expert Team Backing Developed by cybersecurity specialists with deep understanding of modern attack vectors
Interested in Testing the Service?
Contact us for immediate access to the Sandbox environment, full technical documentation with request/response examples, and start integrating PhishIQ within your organization or platform in just a few days.


