In 2026, phishing is no longer template-based. It has become automated, dynamic, and personalized at scale.
A recent study conducted by our research team, Team51, reveals a structural shift in how malicious campaigns are created, deployed, and optimized in real time.
Key Findings
After analyzing active phishing campaigns and malicious infrastructures, we found that:
- 72% of the campaigns analyzed included content generated using advanced language models
- The average time required to generate a phishing landing page tailored to a specific organization was under 10 minutes
- 58% of highly personalized campaigns successfully bypassed traditional email filtering systems
- Domain and infrastructure rotation now occurs within hours rather than days
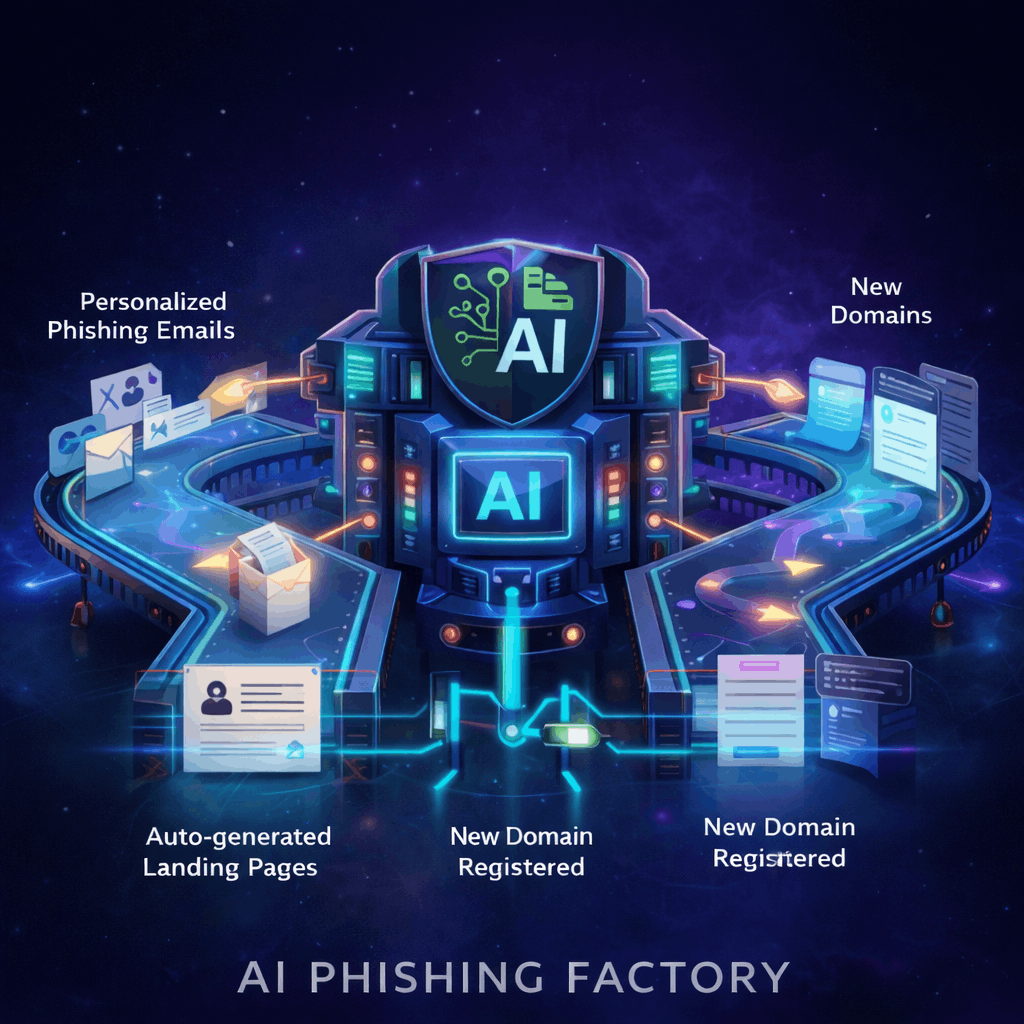
How Attackers Use AI
Dynamic Content Generation
Messages tailored to job roles, industry terminology, language preferences, and internal communication style.
Automated Personalization at Scale
Use of publicly available data to craft targeted messages for individual employees.
Real-Time Landing Page Generation
Rapid cloning of legitimate websites, adaptation to corporate branding, and iterative changes based on victim interaction.
Infrastructure Rotation and Evasion
Abuse of legitimate cloud services, short-lived domains, and constantly shifting redirect chains.
Strategic Implications
When AI generates dynamic, personalized threats within minutes, static detection mechanisms are no longer sufficient.
The challenge is no longer identifying a known malicious domain.
It is understanding intent, context, and behavior in real time — before the click.