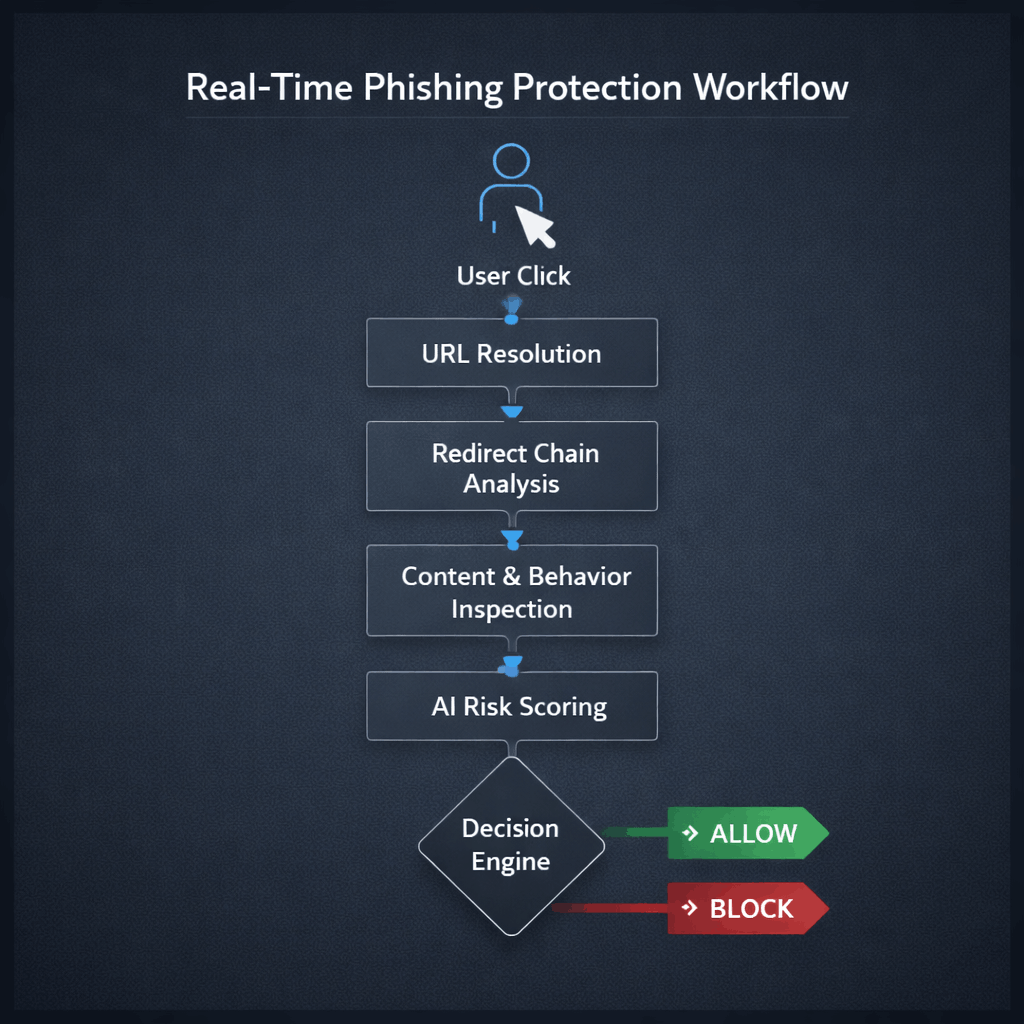
Unlike traditional email filtering or static URL blocklists, real-time protection operates at click time, evaluating the full execution path of a URL before allowing the session to proceed.
This approach is built on dynamic inspection, behavioral analysis, and instant risk scoring — not historical reputation alone.