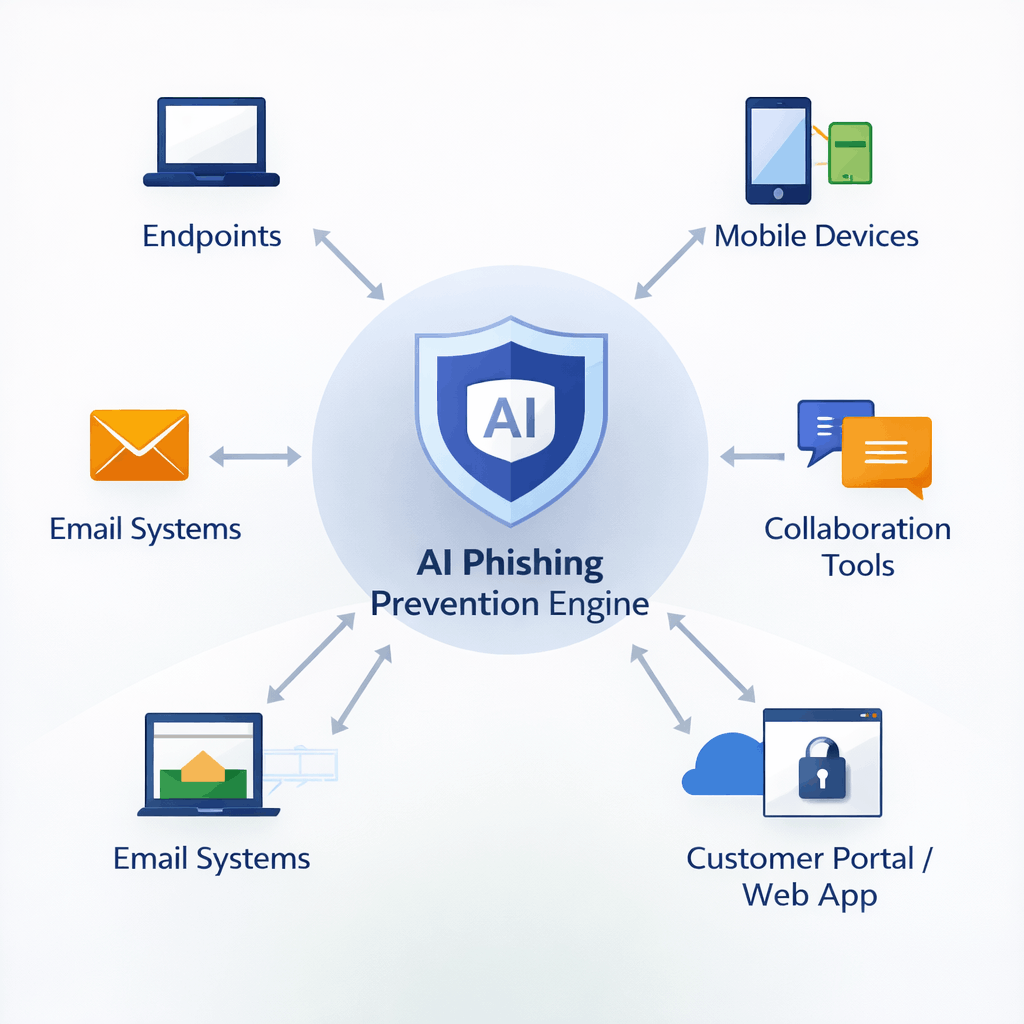
Phishing attacks no longer target only corporate email. Modern campaigns exploit endpoints, mobile devices, SaaS applications, collaboration tools, and even customer-facing portals. Enterprise phishing defense architecture must therefore be distributed, scalable, and prevention-driven.
This section outlines how to design a scalable enterprise phishing protection framework that operates across the entire digital attack surface.