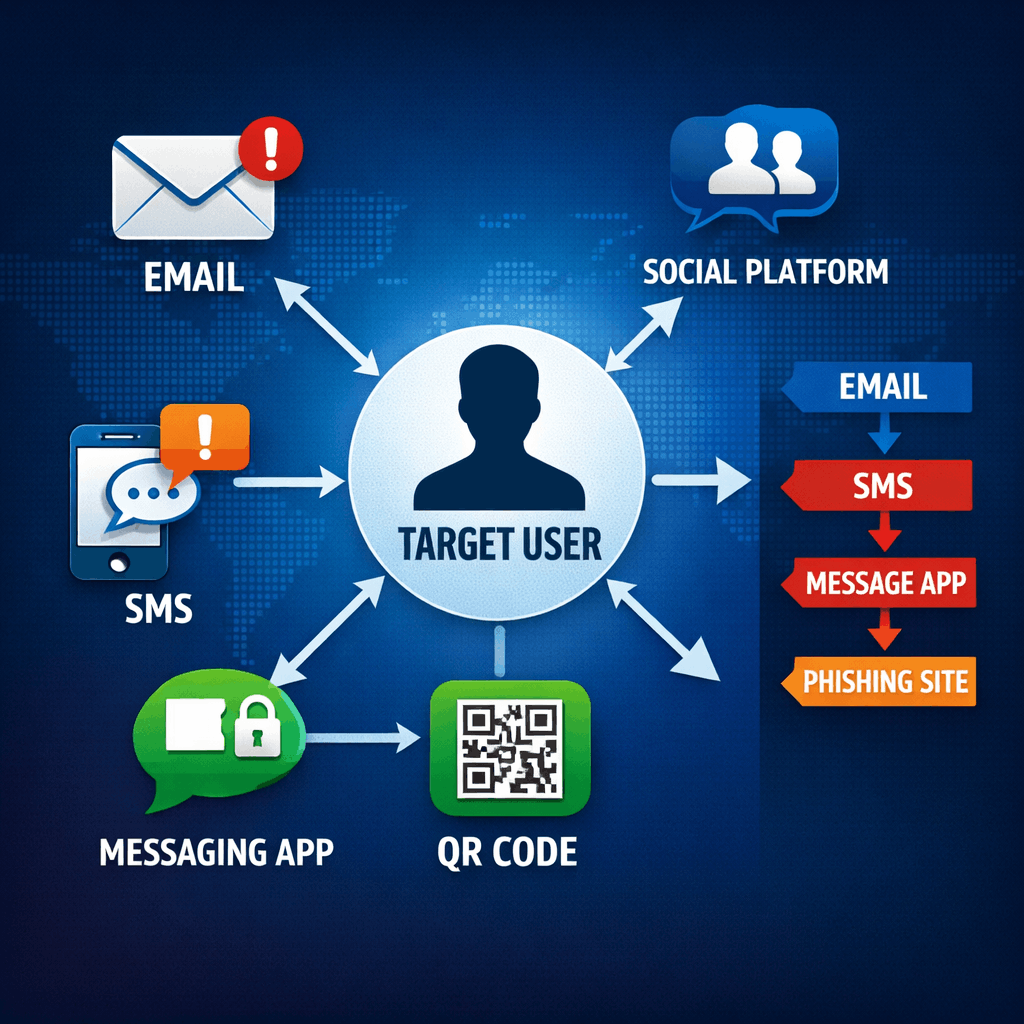
An increasing number of campaigns are intentionally designed as multi-channel operations, combining SMS, messaging applications, social networks, and SaaS platforms as part of a coordinated attack strategy.
Smishing has evolved from a standalone text message into a component within a broader attack chain. Instead of a single interaction, attackers create a sequence — for example, an initial email followed by a short SMS that introduces urgency and directs the target to a mobile-optimized phishing page.
Research Findings
In studies conducted beginning in October 2025, in collaboration between our research team and additional research groups, thousands of attack interactions across multiple sectors — including finance, technology, and healthcare — were analyzed. The research focused on live campaigns and examined cross-channel transition patterns, timing intervals, and interaction rates.
The findings revealed that:
- More than 45% of the campaigns analyzed involved at least two attack channels
- Multi-channel campaigns demonstrated interaction rates significantly higher than single-channel campaigns
- When an SMS was delivered shortly after an email, click rates increased measurably
- Campaigns tailored to an employee's role or organizational context achieved higher response rates
The conclusion was consistent: the sequence between channels creates a perception of legitimacy that reduces suspicion.
The Defensive Challenge
Most security solutions operate in silos. An email security system is not necessarily correlated with SMS monitoring or activity across other platforms. When each interaction is evaluated independently, it becomes difficult to identify the broader pattern of a coordinated attack.
The shift toward multi-channel phishing requires cross-channel protection based on behavioral correlation and full contextual awareness - not isolated filtering of a single message.