For years, security systems have relied on blocklists as a primary defense mechanism against malicious phishing sites. However, a recent study conducted by our research team, Team51, indicates that this approach is losing effectiveness against dynamic phishing infrastructures.
Key Findings
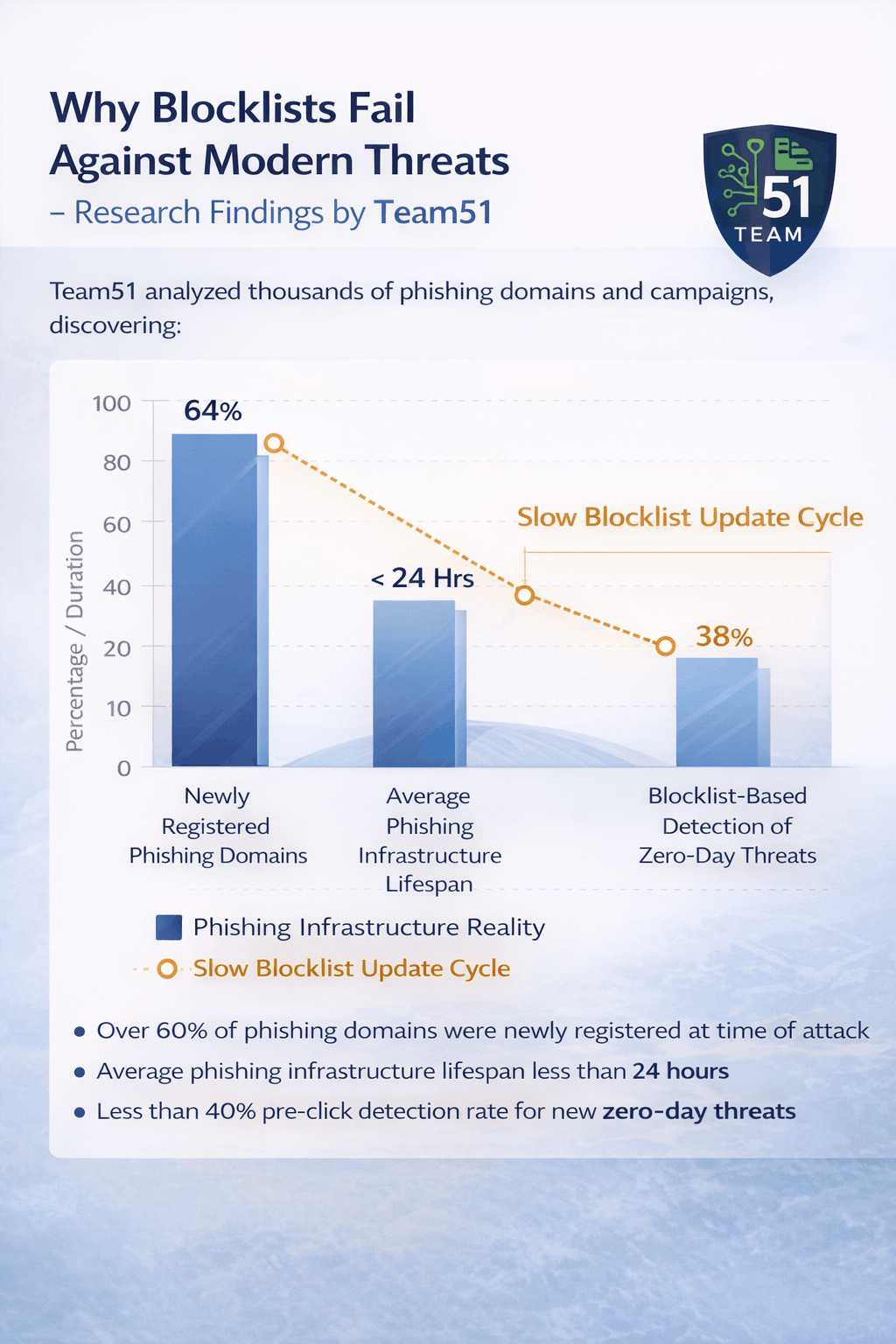
After analyzing thousands of malicious domains and active campaigns, Team51 found that:
- Over 60% of active phishing domains were newly registered at the time of distribution and therefore did not appear on any blocklist
- The average lifespan of phishing infrastructure has dropped to less than 24 hours
- Advanced campaigns use redirect chains to bypass static filtering mechanisms
- The use of fast-flux hosting and legitimate cloud environments makes IP-based detection significantly more difficult
The Structural Limitation of Blocklists
Blocklists operate reactively. A malicious site must first be discovered, analyzed, added to a list, and then distributed to endpoint systems. This process is significantly slower than the rate at which phishing infrastructures are created and rotated.
In practice, there is a critical time gap between threat emergence and mitigation. During that window, users remain exposed.
Impact on Detection Accuracy and Response Time
Team51 measured that in models relying solely on blocklists:
- Pre-click detection rates dropped below 40% for zero-day threats
- The average response time for adding a malicious domain to a blocklist ranged from several hours to multiple days
- False negative rates were significantly higher in short-lived attack campaigns
Conclusion
In an environment where phishing infrastructure is deployed and dismantled within hours, static blocking mechanisms are no longer sufficient.
Effective protection requires real-time analysis, dynamic risk scoring, and decision-making at the moment of click — before users submit sensitive information.