As phishing campaigns scale through automation, traditional reputation-based defenses fail to keep pace. Artificial intelligence and machine learning models now form the foundation of modern phishing detection, enabling predictive identification of zero-day and previously unseen threats.
What Is AI-Based Malicious Link Detection?
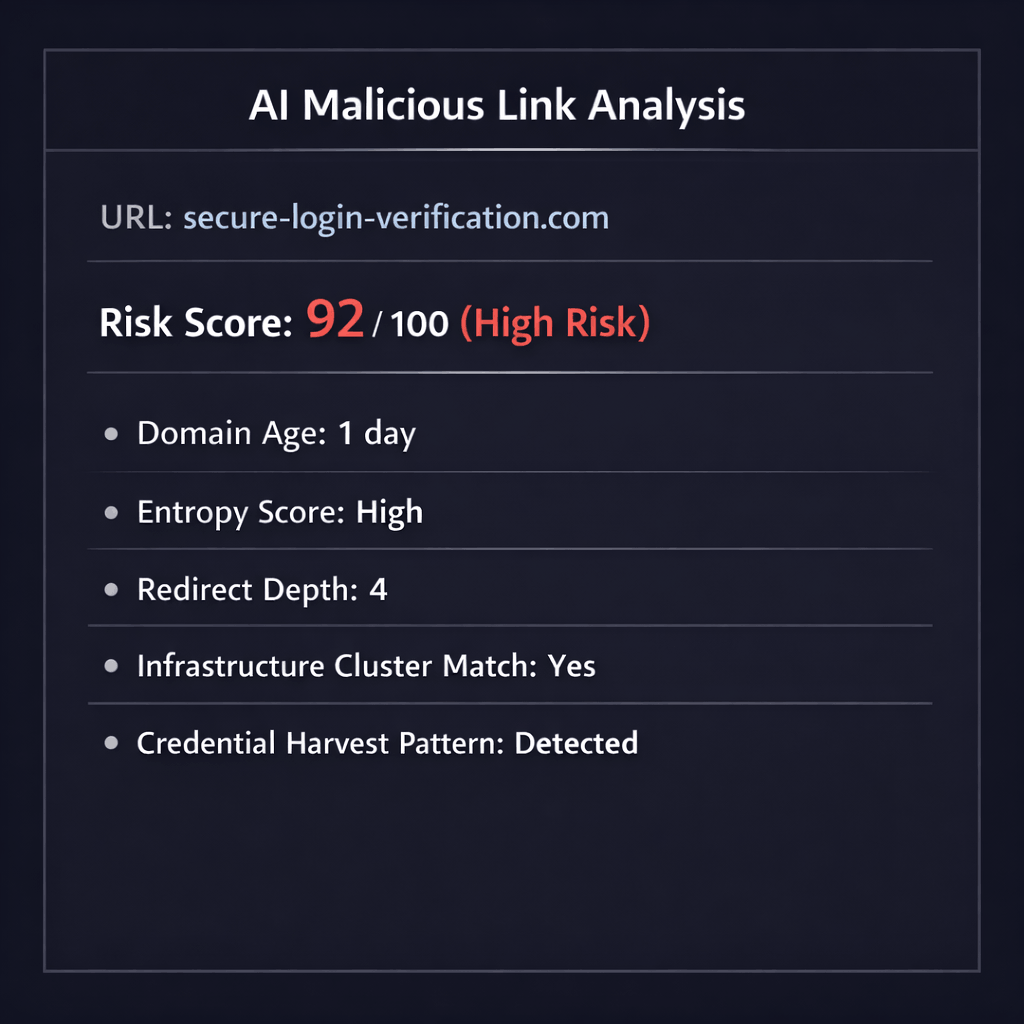
AI-based malicious link detection is the use of machine learning models to analyze URL structure, hosting infrastructure, behavioral patterns, and page content in order to determine whether a link is likely to be phishing or malicious.
Unlike blacklist systems that rely on prior knowledge, AI models evaluate risk probabilistically. They detect patterns associated with phishing infrastructure, even when the domain or payload has never been observed before.
This shift from reactive to predictive detection is critical in today's threat landscape.
The Shift from Signature-Based to Predictive Detection
Legacy phishing detection relied on:
- Domain reputation databases
- Static blacklists
- Known phishing templates
- Manual threat intelligence updates
These methods struggle against:
- Newly registered domains
- Disposable phishing infrastructure
- Polymorphic phishing kits
- AI-generated content variations
AI detection reframes the question.
Instead of asking, "Is this URL known to be malicious?"
The system evaluates, "Does this URL behave like phishing infrastructure?"
This predictive approach dramatically reduces exposure to zero-day phishing attacks.
Machine Learning Feature Extraction: What the Model Analyzes
Effective AI phishing detection begins with structured feature extraction across multiple technical layers.
1. URL-Level Signals
Machine learning models evaluate:
- Domain age and registration metadata
- Character entropy and randomness
- Subdomain abuse patterns
- Typosquatting indicators
- Homograph attacks
These features help detect suspicious domains before page content is rendered.
2. Hosting and Infrastructure Analysis
Phishing campaigns often reuse operational tactics even when domains change.
AI models assess:
- Autonomous System Number anomalies
- Hosting churn velocity
- Certificate issuance inconsistencies
- Shared IP risk clusters
- CDN abuse patterns
Infrastructure analysis enables detection of malicious link networks rather than isolated domains.
3. Content and Structural Analysis
When content is rendered, AI systems evaluate:
- DOM structure similarity to credential harvesting templates
- Hidden form fields and credential capture logic
- Script obfuscation patterns
- External resource loading behavior
- Brand impersonation markers
This allows detection of phishing pages even when visual layouts are modified.
4. Behavioral Detection
Behavioral modeling is often the strongest phishing indicator.
AI systems analyze:
- Redirect chain depth and anomalies
- Conditional payload delivery
- Geo-targeting logic
- User-agent fingerprinting
- Time-delayed activation mechanisms
Behavior reveals intent even when surface indicators appear legitimate.
Detecting Zero-Day and Unknown Phishing Infrastructure
Zero-day phishing domains have no historical reputation.
Traditional filters typically miss them.
AI models detect zero-day threats by:
- Clustering structural similarities across campaigns
- Identifying statistically abnormal infrastructure patterns
- Learning behavioral fingerprints of phishing kits
- Assigning probabilistic risk scores in real time
This enables detection within minutes of infrastructure activation, often before large-scale victim exposure.
Pre-Click vs Click-Time AI Detection
Modern malicious link detection operates in multiple phases.
Pre-Click AI Analysis
Links can be analyzed before user interaction when they are:
- Received via email
- Shared in collaboration platforms
- Submitted through APIs
- Indexed inside SaaS environments
Pre-click detection evaluates structural and infrastructure signals early, enabling proactive risk classification.
Click-Time Deep Inspection
Some phishing payloads activate only upon user interaction.
Click-time AI expands detection to include:
- Live redirect tracing
- Dynamic content rendering
- Execution-time behavioral inspection
Combining pre-click AI detection with real-time phishing protection at click time creates layered, enterprise-grade defense.
Continuous Learning and Model Adaptation
Phishing tactics evolve continuously.
Enterprise AI detection systems require:
- Ongoing model retraining
- Feedback loops from blocked attacks
- Threat intelligence enrichment
- Adversarial testing
Without continuous adaptation, detection accuracy degrades as attacker techniques evolve.
Why AI Is Essential for Malicious Link Detection
The scale of modern phishing exceeds manual review capacity. Attackers automate:
- Domain generation
- Infrastructure rotation
- Template variation
- Content mutation
AI-powered malicious link detection provides:
- Early identification of phishing campaigns
- Reduced reliance on reputation databases
- Scalable analysis across millions of URLs
- Predictive detection of unknown threats
In today's threat landscape, AI is not an enhancement. It is the core detection engine.
Frequently Asked Questions
How does AI detect malicious links?
AI models analyze URL structure, hosting infrastructure, behavioral indicators, and content anomalies. These signals are processed through machine learning algorithms to generate probabilistic risk scores in real time.
Can AI detect zero-day phishing domains?
Yes. By identifying structural, infrastructural, and behavioral similarities across campaigns, AI systems can flag phishing domains even when they have no prior reputation history.
Is AI-based phishing detection better than traditional blacklists?
AI detection complements and often outperforms blacklists by identifying previously unseen threats. Blacklists rely on historical data, while AI models evaluate risk patterns dynamically.
Conclusion
AI-based malicious link detection transforms phishing defense from reactive filtering to predictive security.
By combining machine learning feature extraction, infrastructure analysis, behavioral modeling, and continuous retraining, organizations can detect phishing URLs before they are widely known, before reputation systems update, and often before users click.
In an ecosystem defined by automation and infrastructure churn, predictive AI detection is foundational to sustainable phishing prevention.

