Team51 research identifies a new attack pattern in which a fully legitimate website undergoes a transformation into malicious behavior during an active session through the use of Generative AI to create code in real time.
Unlike traditional attacks that rely on static payloads, compromised pages, or embedded malicious files, in this model the page loads without any suspicious components. Only after loading does it initiate a call to a Generative AI API, which produces dynamic JavaScript that is immediately injected and executed within the user’s browser context.
The malicious code is not pre-hosted, is not part of the original content, and cannot be detected prior to execution.
Mechanism Characteristics
Analysis revealed a consistent operational pattern:
- Loading of a legitimate website with no prior modification
- A concealed request to a Generative AI service
- Real-time generation of malicious JavaScript
- Injection and execution within the active session
During static inspection, the website appears entirely benign.
The transformation occurs solely at the behavioral level during runtime.
Structural Difference from Existing Models
In conventional web attacks, at least one of the following is typically observable:
- A suspicious domain
- A known signature
- A static malicious file
- A dedicated phishing page
In this model:
- No static payload exists
- No reusable signature is present
- No malicious component exists prior to execution
- The domain itself may be fully legitimate
The page is not malicious by virtue of its content, but becomes malicious through an external and dynamic generation process in real time.
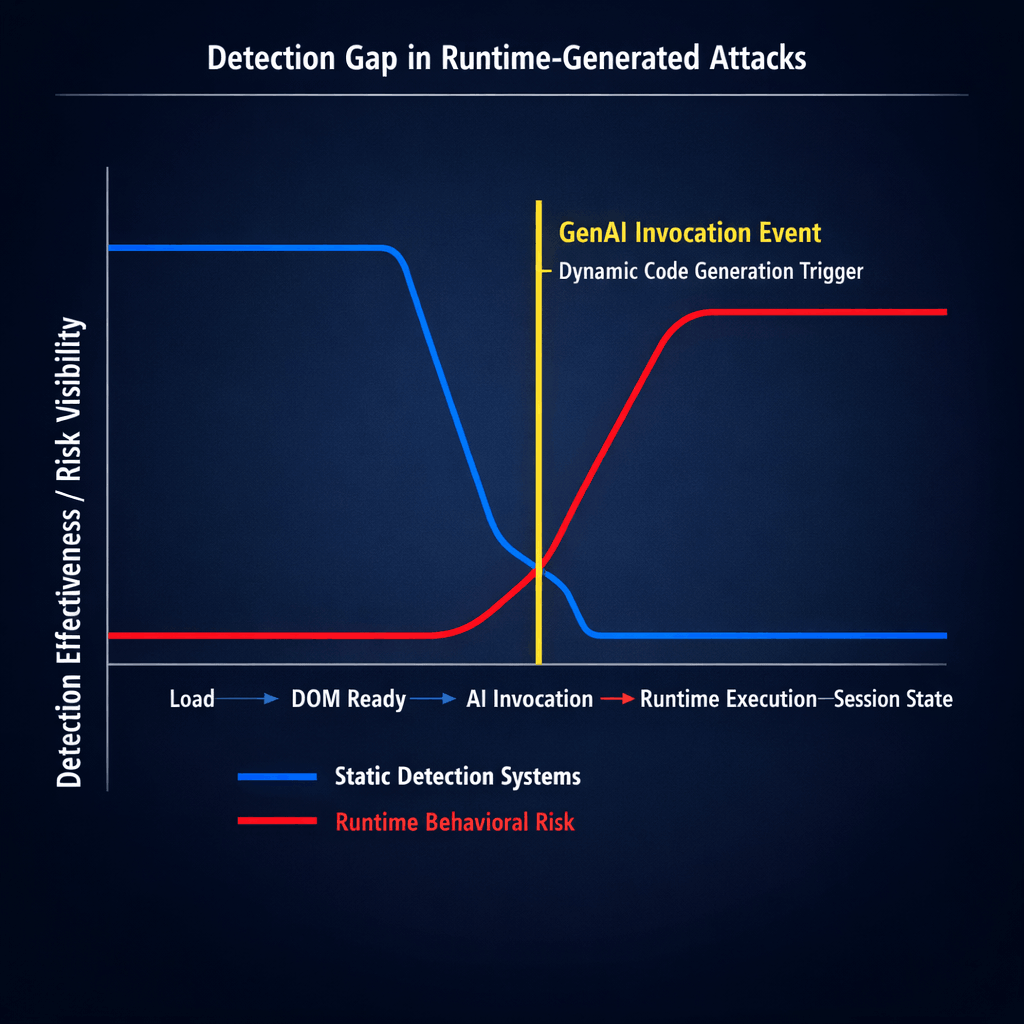
Implications for Detection Mechanisms
Team51 findings indicate that:
- Static scanning mechanisms detect no anomalies at load time
- Signature-based systems are ineffective against per-session generated code
- Domain reputation controls provide limited protection
- Detection becomes possible only through real-time behavioral and session-level analysis.
Conclusion
The use of Generative AI to produce malicious logic at runtime represents a structural shift in the threat landscape.
This model moves from infrastructure-based attacks to dynamically generated attack logic, where the malicious component does not exist until the moment of execution.
The early detection window is significantly reduced, requiring defensive strategies to evolve toward real-time behavioral monitoring and session-aware protection.