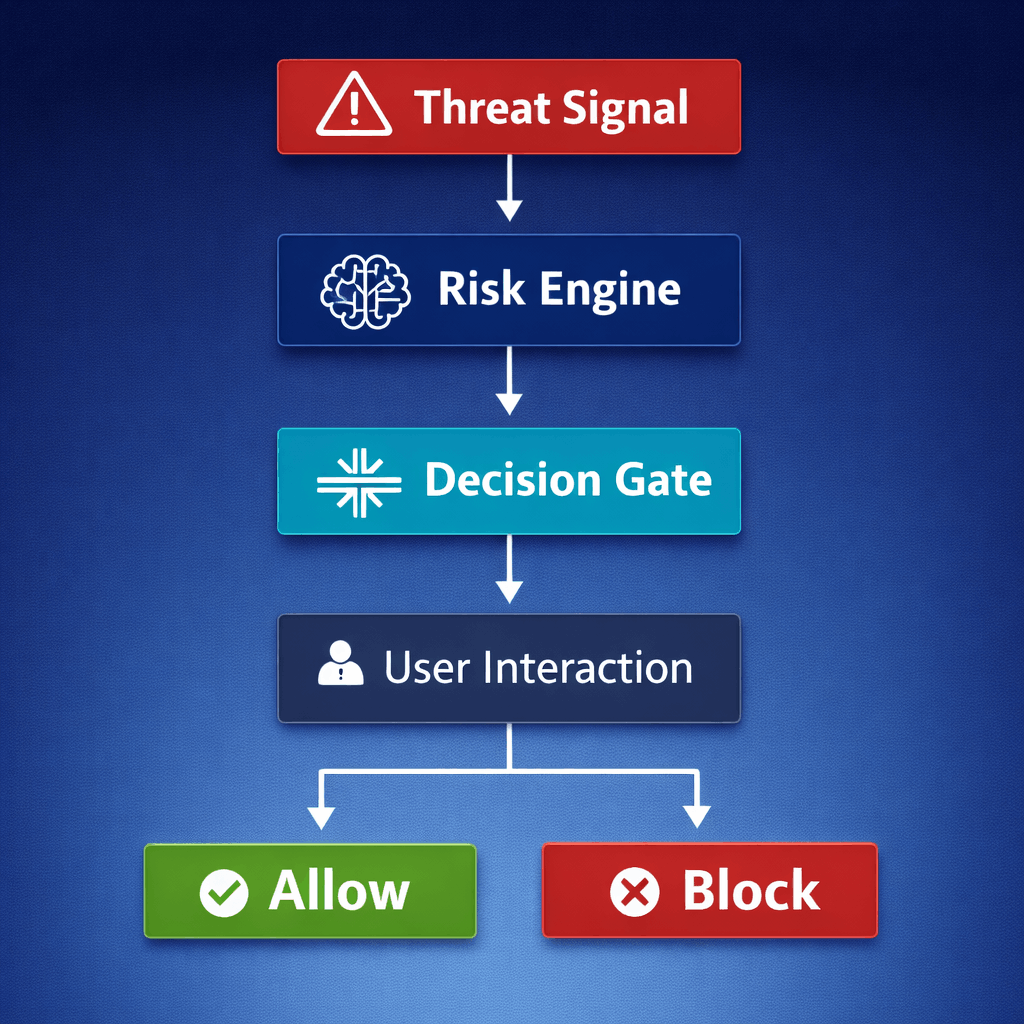
Most phishing protection solutions operate at the moment of user interaction. The implicit assumption is that the system will inspect and analyze the destination once the user clicks.
However, in distributed, SaaS-driven, and highly dynamic environments, this model positions security in a reactive posture rather than a control posture.
Once the user clicks:
- An outbound connection is initiated
- Malicious infrastructure is engaged
- A browser session may be exposed
- A critical time window opens
Even if the decision is made quickly, the transition to interaction has already occurred.
The architectural implication is clear: Click-time is a late control point.