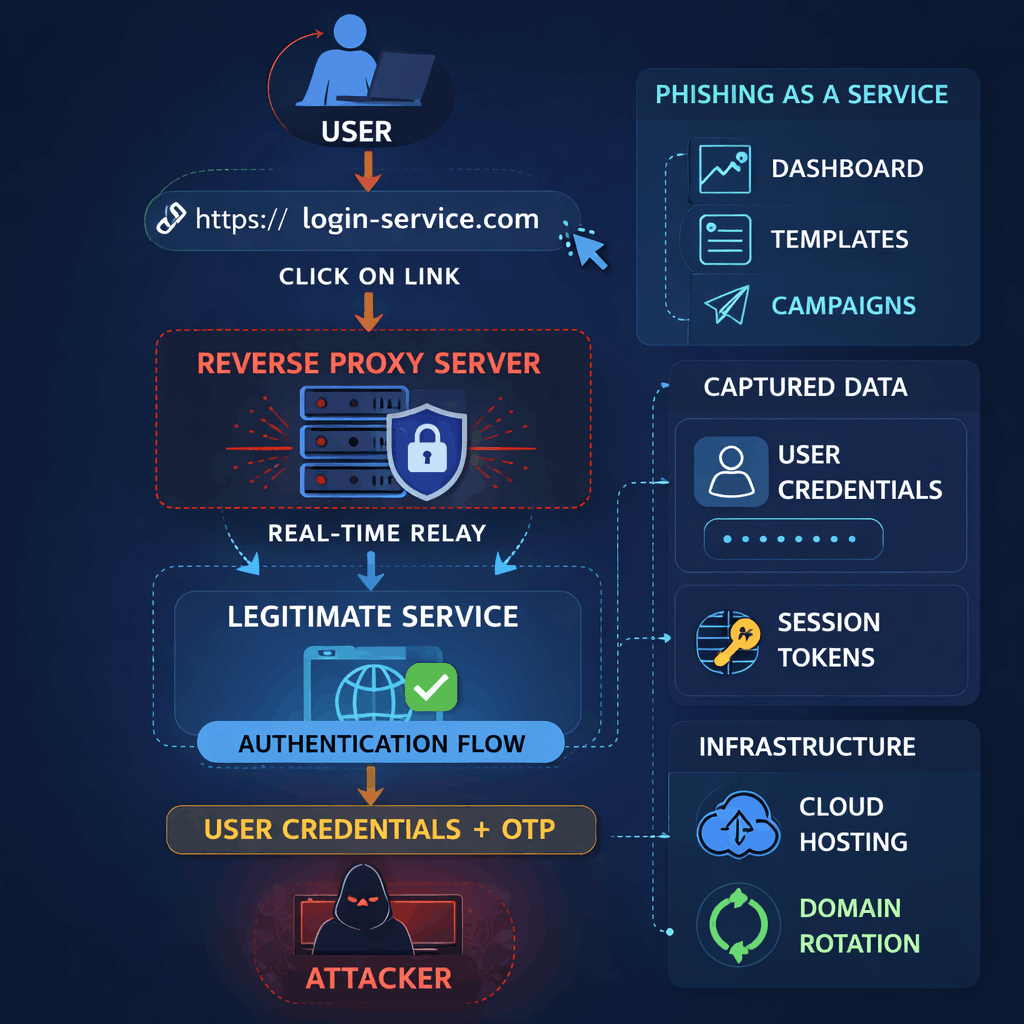
In recent years, there has been a measurable increase in the use of reverse proxy based phishing kits across enterprise and consumer targeted campaigns. Unlike traditional static phishing pages, these infrastructures act as real time intermediaries between the victim and the legitimate service, presenting authentic login pages while intercepting credentials and session data during the authentication process.
Team51, the dedicated research team behind RedFox Enterprise Solutions, conducted an analytical study examining active campaigns, Phishing as a Service infrastructures, and techniques designed to bypass multi factor authentication controls.
Research Scope and Methodology
Team51 analyzed active phishing infrastructures, observed live authentication relays, and reviewed operational patterns across commercially distributed Phishing as a Service platforms. The research focused on architectural design, deployment speed, detection evasion mechanisms, and impact on authentication security controls.
Key Findings
After examining active infrastructures and ongoing campaigns, Team51 found that:
- Over 70 percent of observed campaigns used reverse proxy techniques to relay authentication sessions in real time
- In more than 60 percent of cases, attackers captured session tokens in addition to user credentials
- Phishing as a Service platforms enabled full campaign deployment in less than one hour from configuration to distribution
- The majority of infrastructures operated on legitimate cloud hosting services, significantly reducing the effectiveness of IP based blocking
- Campaign operators frequently rotated domains and infrastructure components to minimize detection windows
Architectural Characteristics of Reverse Proxy Phishing
Reverse proxy phishing infrastructures differ fundamentally from static phishing kits.
In this model:
- The phishing server establishes a live connection with the legitimate service
- The victim interacts with the genuine login interface in real time
- Credentials and one time authentication codes are relayed to the legitimate platform
- Session tokens are intercepted and stored by the attacker
Because the authentication flow completes successfully against the real service, standard validation signals such as valid certificates, correct branding, and expected user experience remain intact.
The Structural Limitation of Traditional Detection Mechanisms
Traditional security systems typically rely on one or more of the following:
- Domain reputation analysis
- Signature based detection
- Static content inspection
- Blocklists updated after threat discovery
In reverse proxy scenarios:
- The domain may be newly registered and short lived
- The hosted infrastructure may appear technically clean
- The login page content is delivered directly from the legitimate service
As a result, security controls observe traffic patterns that resemble normal authentication activity, while credential interception occurs within the relay channel between the user and the legitimate platform.
Impact on Detection Rates and Response Time
Team51 measurements indicate that:
- Pre click detection rates decline significantly when real time proxying is employed
- One time password based multi factor authentication does not prevent account takeover when session tokens are captured
- Infrastructure lifespans often fall below traditional blocklist update cycles
- Reactive mitigation approaches introduce critical exposure windows during active campaigns
These findings demonstrate that reverse proxy based phishing reduces the reliability of static or reputation driven defenses.
The Operational Shift to Phishing as a Service
The commercialization of reverse proxy kits has accelerated adoption.
Phishing as a Service models provide:
- Subscription based access to ready made infrastructure
- Administrative dashboards for campaign management
- Automated credential harvesting and session storage
- Technical support and regular updates
This service oriented model lowers the technical barrier to entry and enables rapid scaling of sophisticated phishing operations.
Conclusion
The reverse proxy based Phishing as a Service model represents a structural evolution in phishing operations. By leveraging legitimate login flows and real time authentication relays, attackers are able to bypass many static detection mechanisms and undermine traditional assumptions about multi factor authentication effectiveness.
In an environment where authentic login pages are integrated into the attack chain, effective protection requires real time analysis and session level anomaly detection during the authentication flow, with decision making occurring within the session itself rather than after compromise.